
What Is Phishing in Crypto? Common Scams and How to Avoid
Share
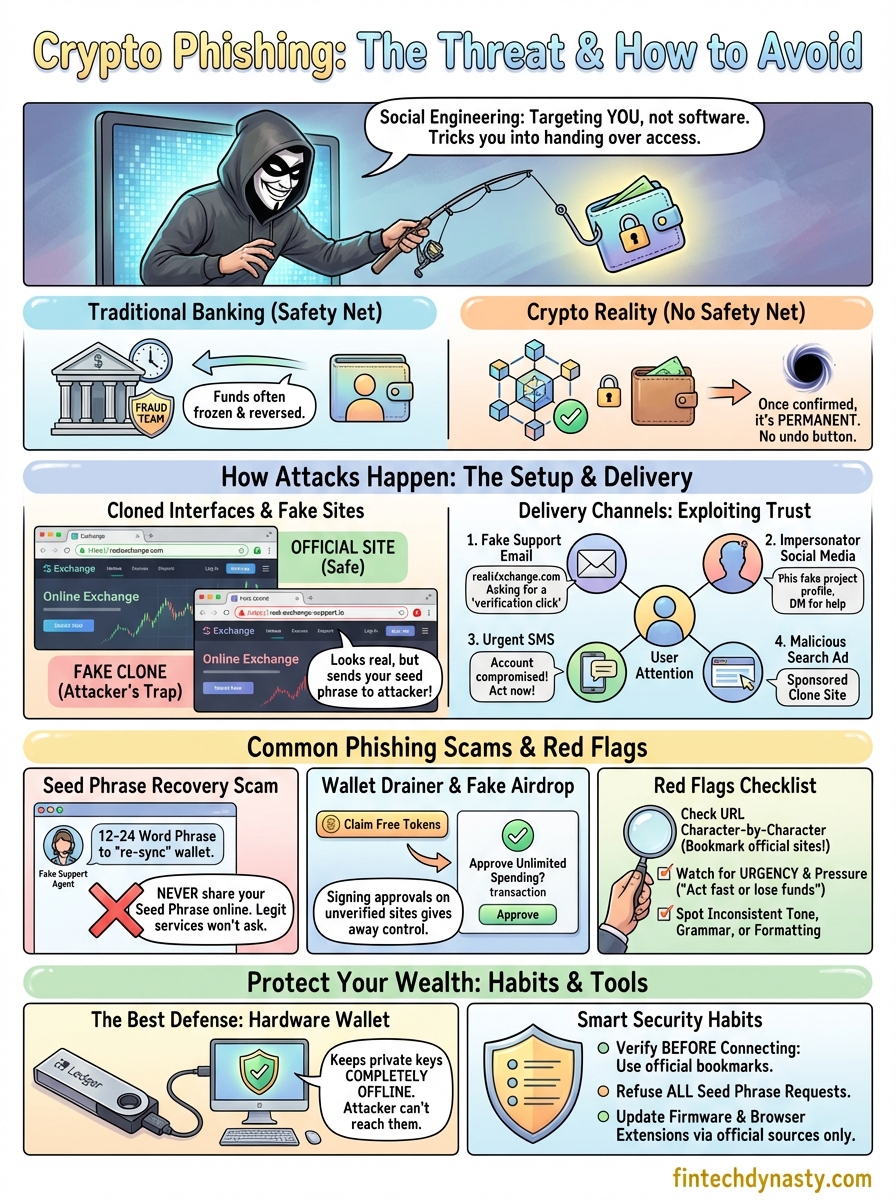
Most crypto isn't stolen through code exploits or brute-force attacks. It's stolen because someone clicked the wrong link, entered their seed phrase on a fake website, or trusted a message that looked legitimate. That's what phishing in crypto really comes down to, social engineering designed to trick you into handing over access to your wallet.
These scams have gotten sharper over the years. Attackers now clone entire exchange interfaces, spoof official support channels, and send targeted emails that reference your actual transaction history. Whether you hold Bitcoin on a hardware wallet or keep assets on an exchange, phishing is the single most common threat to your funds. And it works because it targets people, not software.
At FinTech Dynasty, we focus on the practical side of protecting your digital wealth through education and proper security habits. This article breaks down exactly how crypto phishing works, walks through the most common attack types you'll encounter, and gives you concrete steps to avoid becoming a target.
Why crypto phishing works
Phishing succeeds in crypto for reasons that don't apply to traditional banking. When someone drains your bank account, a fraud team can often freeze assets and reverse the transaction within hours. In crypto, no such safety net exists. The moment funds leave your wallet, the transaction is permanent, and no customer service line can undo it. That gap between user expectation and reality is exactly what attackers count on.
Once a crypto transaction is confirmed on the blockchain, it cannot be reversed by any person, company, or government.
The knowledge gap attackers exploit
Most people who hold crypto still don't fully understand how private keys and seed phrases work. They know they own Bitcoin or Ethereum, but they don't know that whoever holds the seed phrase controls the wallet entirely. Attackers know this. Phishing campaigns often focus specifically on getting you to type those 12 or 24 recovery words into a form, because that single action transfers complete, permanent control of your funds to someone else. When you understand what is phishing in crypto, you start to see it's less about breaking technology and more about exploiting this gap.
Your unfamiliarity with normal platform behavior also works against you. If you have never seen what a legitimate hardware wallet support email looks like, you have no baseline to compare it against. Attackers replicate logos, fonts, and email formatting with enough accuracy that spotting the fake requires deliberate, focused attention, not a quick glance.
Why urgency and fear drive clicks
Urgency is the attacker's most reliable tool. A message that says "Your wallet has been compromised, verify your recovery phrase within 24 hours or lose access" bypasses the part of your brain that evaluates risk. Instead of pausing to verify, you react. Crypto users are particularly vulnerable here because the financial stakes feel enormous and the ecosystem is complex enough that an unexpected security alert seems entirely plausible.
Fear of losing assets is equally effective. Attackers craft messages around scenarios that feel just believable enough, a suspicious login, an unrecognized transaction, a forced account migration. These scenarios mirror real events that do happen on exchanges and wallets, which makes the scam harder to dismiss outright. The emotional response is fast, and that speed is the entire point.
How crypto phishing attacks happen
Every phishing attack follows a similar structure: an attacker builds a convincing fake, delivers it through a channel you trust, and captures your credentials or wallet access before you realize anything is wrong. Understanding what is phishing in crypto at a mechanical level helps you recognize the setup before you fall into it.
Fake websites and cloned interfaces
Attackers build near-perfect replicas of legitimate crypto platforms, from exchanges like Coinbase to hardware wallet brand sites like Ledger or Trezor. The URL is usually the only visible difference, a swapped letter, an added hyphen, or a different domain extension. Once you land on the page and enter your seed phrase or private key, that data goes directly to the attacker, not to any real wallet recovery system.

A cloned website can look identical to the real one down to the copyright footer, but a single character difference in the URL means you are on an attacker's server.
How attackers deliver the bait
Multiple delivery channels exist because attackers adapt to wherever you spend your attention. Email, social media, and search ads are the most common routes, but the method always serves the same purpose: get you to a controlled page or conversation where you hand over access.
- Email: Spoofed sender addresses that mimic official platform addresses
- Social media and Discord: Fake support accounts or impersonated project members
- SMS: Messages referencing your account activity or a pending security alert
- Search ads: Paid results that appear above legitimate sites and link to clone pages
Each channel exploits a different layer of trust you have already built with a platform or community. The delivery vehicle changes, but the outcome the attacker wants stays exactly the same.
Common crypto phishing scams to know
Understanding what is phishing in crypto gets more practical when you can name the specific tactics attackers use. Each scam type targets a different behavior, but they all move toward the same goal: capturing your seed phrase, private key, or exchange login before you realize anything is wrong.
Seed phrase recovery scams
These are among the most direct attacks you will encounter. An attacker contacts you through email, fake support chat, or Discord and claims your wallet needs to be "verified" or "re-synced." They send you to a form requesting your 12 or 24-word seed phrase. No legitimate wallet company, hardware manufacturer, or exchange will ever ask you to submit your recovery phrase online for any reason.
If you receive this request, treat it as a scam regardless of how official it looks. Attackers clone real support interfaces and mirror language pulled directly from actual help documentation to make the request feel routine and trustworthy.
Wallet drainer and fake airdrop scams
These attacks reach you through fake token giveaways or project announcements that prompt you to connect your wallet to a malicious site. Once connected, you sign a transaction that grants the attacker unlimited spending approval for your tokens. Your wallet can be emptied without you entering a single password or seed word.
Signing an approval transaction on an unverified site can hand complete control of your tokens to an attacker without them ever asking for your seed phrase.
Some versions of this scam spread through compromised Discord servers or spoofed social media accounts that appear to belong to legitimate crypto projects. The link looks credible because it comes from a source you already follow, which is exactly what makes this one of the harder scam types to dismiss on instinct.
How to spot crypto phishing red flags
Knowing what is phishing in crypto is only useful if you can catch it in real time. Most phishing attacks reveal themselves before any damage is done, but you have to look at the right details. The red flags are almost always present; they are just easy to miss when you are moving quickly or feeling pressured.
Check the URL before you type anything
The URL is the most reliable signal you have before entering any credentials or connecting your wallet. Look at the full domain, not just the visual branding on the page. Attackers register addresses like "ledger-support.io" or "myetherwalet.com" that read as legitimate at a glance but point to servers they control entirely.
Before typing your seed phrase or wallet password anywhere, copy the URL and compare it letter by letter against the official domain you normally use.
Bookmark the real versions of every platform you use regularly. Always navigate from your bookmark rather than from a link in an email, social post, or search result. This single habit eliminates the most common delivery route attackers use.
Watch for pressure and mismatched communication
Urgency is a reliable signal that something is wrong. Legitimate platforms do not send messages demanding you verify your recovery phrase within hours or threatening immediate account loss. If a message is pushing you to act fast, slow down instead.
Pay attention to inconsistencies in tone and formatting as well. Official support emails use consistent sender domains, reference your actual username, and never ask for private keys or seed words. Scam messages often contain subtle grammar issues, generic greetings, or sender addresses that differ from the official domain by a single character. These mismatches are your clearest warning that the message did not come from who it claims.
How to protect your wallet from phishing
Spotting red flags helps, but building habits that limit your exposure before an attack reaches you matters more. The most effective defenses against phishing don't require technical expertise. They require consistent, deliberate behavior every time you interact with your wallet or any crypto platform.
Use a hardware wallet for long-term storage
A hardware wallet keeps your private keys completely offline, which means a phishing site or malicious approval transaction cannot reach them through a browser or internet connection. Even if an attacker tricks you into visiting a fake site, they cannot extract keys that never touch the internet. This is the strongest single step you can take to protect significant holdings.
A hardware wallet signs transactions internally, so your private key never leaves the device, even when you confirm a transaction on screen.
Understanding what is phishing in crypto also means understanding why cold storage removes the most common attack vector entirely. When your keys stay offline, the window attackers have to work with shrinks considerably.
Verify before you connect or submit
Before you connect your wallet to any site or submit any information, open the official website directly from your bookmark, not from a link sent to you. Cross-check the URL character by character. If a site, email, or message asks for your seed phrase under any circumstances, close it immediately. No legitimate service ever needs that information.
Keep your wallet firmware and browser extensions updated through official channels only. Outdated software creates vulnerabilities attackers can layer on top of a phishing attempt. Download updates only from the hardware manufacturer's verified website, and never from a link inside an email or a direct message.
Quick wrap-up and what to do next
Phishing is the most common way crypto holders lose funds, and understanding what is phishing in crypto puts you ahead of most targets attackers pursue. The attack relies on urgency, fear, and the convincing appearance of trusted platforms. It does not require breaking any code, just a fake page, a pressured moment, and your attention pointed in the wrong direction.
Building real protection means combining awareness with the right tools. A hardware wallet keeps your private keys completely offline, removing the most dangerous attack vectors entirely. Verifying URLs, refusing any request for your seed phrase, and navigating from bookmarks rather than links closes the gaps that phishing campaigns depend on. You do not need to be a technical expert to stay protected.
If you want to compare hardware wallets and build a complete security setup, start your research at FinTech Dynasty, where every guide focuses on practical protection, not price speculation.
