
How Phishing Works: Anatomy of a Scam and How to Spot It
Share
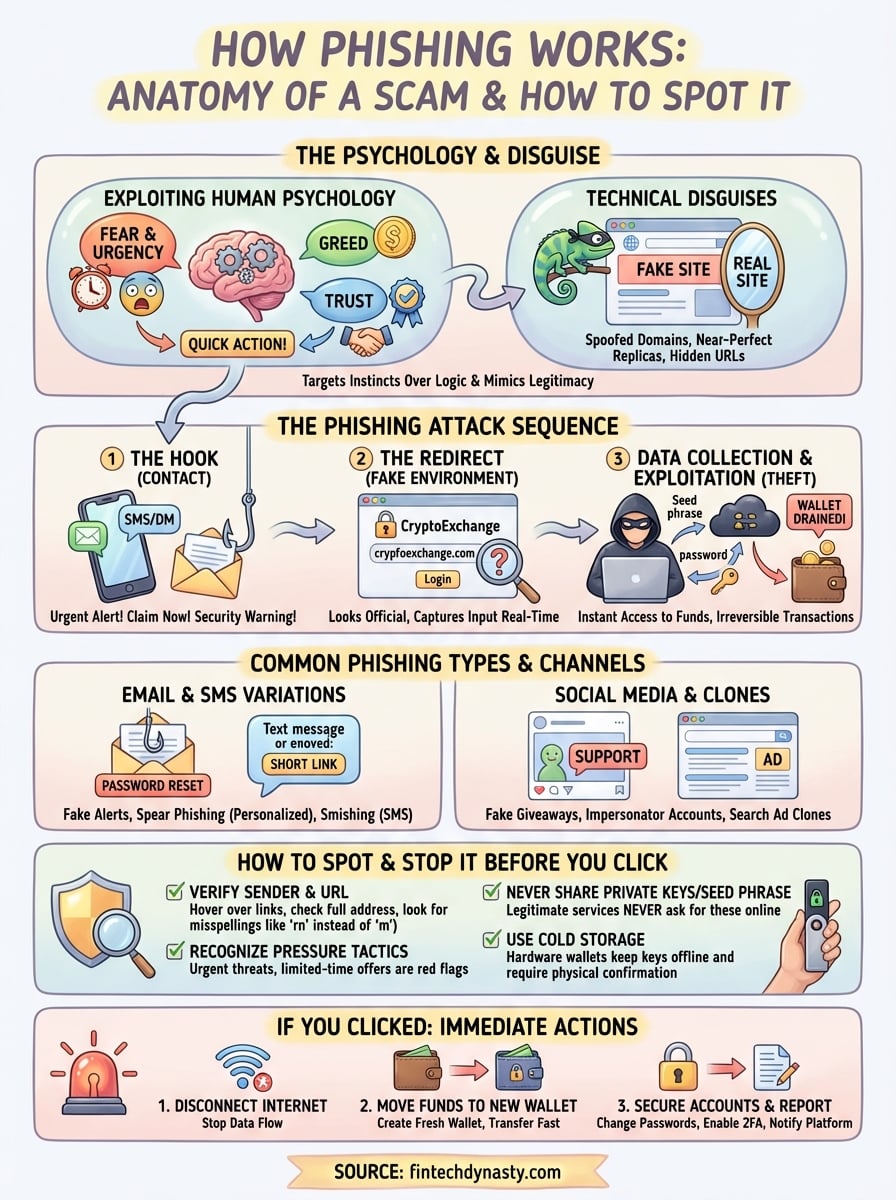
Your private keys, your exchange login, your seed phrase, phishing attacks target all of them. And unlike the clumsy scam emails of the past, modern phishing campaigns are sophisticated, personalized, and disturbingly effective. Understanding how phishing works gives you the foundation to recognize these attacks before you become a victim.
For cryptocurrency holders, the stakes are higher than most realize. A single successful phishing attempt can drain an entire wallet in seconds, with no bank to reverse the transaction and no customer service to call. This is why self-custody education at FinTech Dynasty always includes a heavy emphasis on threat awareness, knowing how attackers operate is just as important as choosing the right hardware wallet.
This guide breaks down the anatomy of a phishing scam from start to finish. You'll learn the psychological tricks attackers use, the technical methods behind their schemes, and the specific red flags that reveal a phishing attempt. By the end, you'll have a practical framework for evaluating suspicious messages, links, and requests, whether they come through email, social media, or fake websites.
Why phishing keeps working
Phishing survives because it exploits human psychology, not just technical vulnerabilities. Attackers understand that your brain makes split-second decisions based on emotion, trust, and perceived urgency. Even security-conscious users fall victim because these scams target your instinctive reactions rather than your technical knowledge. When you see a message that appears to come from your exchange warning of suspicious activity, your first impulse is to protect your account, not to analyze the sender's email header.
The psychological advantage
Fear, greed, and urgency remain the most effective psychological triggers in phishing campaigns. Attackers craft messages that make you feel something immediately: panic that your account will be locked, excitement about a token airdrop, or worry that you'll miss a limited-time opportunity. These emotional hooks bypass your rational thinking and push you toward quick action before careful evaluation. When an email claims your wallet will be frozen in 24 hours unless you verify your seed phrase, the stress response overrides the obvious red flag.
Social proof and authority also manipulate your decision-making. Scammers impersonate trusted brands like Coinbase, Ledger, or MetaMask because your brain associates those names with legitimacy. You're less likely to question a message that appears to come from a source you already trust. This is why understanding how phishing works requires recognizing that your own trust mechanisms become weapons against you. The same instinct that helps you navigate legitimate services makes you vulnerable when attackers fake the appearance of authority.
Attackers win when they create situations where your emotional response is faster than your security awareness.
Technical disguises become harder to detect
Modern phishing sites replicate official websites with near-perfect accuracy. Attackers copy the exact design, branding, logos, and even functional elements like password fields and two-factor authentication prompts. You might notice nothing wrong at first glance because these fake sites mirror every visual detail of the legitimate platform. The only difference often appears in the URL, and even that can be disguised through techniques like homograph attacks (using characters from different alphabets that look identical).
Email spoofing and domain manipulation make sender verification difficult for average users. Phishers register domains that differ by one letter (ledger-support.com instead of ledger.com) or use subdomains that appear legitimate (secure.verification.google-users.com). Your email client might show a display name of "Ledger Support Team" while hiding the actual sending address in the background. Without checking the full header information, you have no way to verify authenticity through casual inspection.
The speed and scale of attacks
Phishing campaigns operate at massive scale with minimal cost. Attackers send millions of messages knowing that even a 0.1% success rate produces hundreds of victims. Automation tools let them launch coordinated attacks across email, SMS, social media, and messaging apps simultaneously. You might receive the same scam through three different channels within hours, each attempt reinforcing the illusion of legitimacy through repetition.
The financial payoff justifies the effort for cybercriminals. A single successful phishing attack against a cryptocurrency holder can yield thousands or millions of dollars in irreversible transactions. Unlike traditional fraud where banks can freeze accounts or reverse charges, stolen crypto transfers immediately and permanently. This high reward-to-effort ratio ensures phishing will continue evolving as long as digital assets exist.
How a phishing scam works step by step
Every phishing attack follows a predictable sequence that you can learn to recognize. Understanding how phishing works from the attacker's perspective gives you the ability to identify the pattern before you reach the dangerous stages. The process moves through distinct phases, each designed to build on the previous one until you've handed over exactly what the scammer wants.

Initial contact and the hook
Attackers establish first contact through a channel you already use regularly. This might be an email that appears to come from your exchange, a direct message on Twitter claiming to be support staff, or a text message about suspicious account activity. The initial message always contains a reason you need to act, whether that's a security alert, a verification requirement, a prize claim, or an urgent policy change that affects your account.
The hook combines urgency with a clear next step. You're told you must verify your identity, confirm a transaction you didn't authorize, or claim tokens before they expire. The message includes a link, a QR code, or instructions to reply with information. Cryptocurrency phishing often uses time pressure ("Your wallet will be locked in 2 hours") or fear of loss ("Suspicious withdrawal detected from your account") to push you toward immediate action.
The initial message works when it triggers your instinct to protect your assets faster than you question the source.
The redirect and fake environment
Clicking the provided link takes you to a website that looks identical to the legitimate platform. Attackers copy every design element, button, form field, and branding detail. You see login screens that mirror MetaMask, hardware wallet verification pages, or exchange security portals. The URL might differ by one character or use a subdomain structure that appears official at first glance.
Data collection and exploitation
The moment you enter information into these fake forms, attackers capture it in real time. If you type your seed phrase, they immediately use it to access your wallet. Login credentials let them drain exchange accounts or change security settings to lock you out. Some sophisticated attacks even display fake loading screens or error messages while the theft occurs in the background, giving you no indication anything went wrong until your funds disappear.
Common phishing types and channels
Phishing attacks arrive through multiple channels, each with distinct characteristics that target different aspects of your online behavior. Attackers constantly adapt their methods based on which platforms you trust most and where you spend your attention. Understanding how phishing works across different channels helps you maintain consistent vigilance regardless of how a scam reaches you.
Email phishing and its variations
Email remains the primary delivery method because it scales easily and users expect to receive account notifications this way. Standard phishing emails impersonate exchanges, wallet providers, or blockchain services with messages about security alerts, account verification, or mandatory updates. You see fake password reset requests, fraudulent transaction confirmations, and warnings about policy violations that all lead to credential harvesting pages.
Spear phishing targets you specifically using information gathered from your social media profiles, public blockchain activity, or data breaches. These personalized attacks might reference your actual wallet address, recent transactions, or participation in specific DeFi protocols. The customization makes them significantly more convincing than mass-distributed scams because they demonstrate knowledge that appears to validate the sender's legitimacy.
SMS and messaging app attacks
Text message phishing (smishing) exploits your mobile device's immediacy. Attackers send alerts about locked accounts, failed verification attempts, or security threats that demand quick action. These messages often include shortened URLs that obscure the destination and make URL inspection nearly impossible on small screens.
Messaging platforms like Telegram and Discord host impersonation scams where attackers clone official support accounts or create fake admin profiles. You might receive direct messages offering help with technical issues or exclusive access to token launches. These platforms make verification difficult because usernames can be duplicated and official verification badges are sometimes faked through clever profile design.
Social media and clone websites
Twitter, YouTube, and other platforms host comment scams where attackers post fake customer service responses under official posts. You see replies offering help or directing you to "resolve issues" through external links. Fake giveaway posts promise token distributions in exchange for sending small amounts first or connecting your wallet to claim rewards.
Phishing succeeds when attackers meet you on platforms you already trust, using interfaces you recognize without question.
Clone websites mirror legitimate services through paid search ads that appear above real results. You search for your hardware wallet's official site and click the first sponsored result without noticing the slightly altered domain, leading you directly into a credential theft operation.
How to spot phishing before you click or sign
Prevention requires active verification before you interact with any suspicious message. Understanding how phishing works gives you the framework to recognize attacks, but applying that knowledge means developing specific checking habits that you perform every time. You catch phishing attempts by examining details that legitimate services get right automatically and scammers struggle to fake perfectly.

Verify the source before you trust the message
Check the full sender address, not just the display name. Hover over the "from" field in emails to reveal the actual sending domain. Legitimate exchanges and wallet providers send from official domains that match their website exactly (support@coinbase.com, not coinbase.security@verify-accounts.net). Look for misspellings, extra words, or unusual domain extensions that indicate impersonation.
Examine URLs before clicking any link by hovering your mouse over them (or long-pressing on mobile) to preview the destination. The URL should match the official website exactly. Attackers use tricks like replacing letters with similar-looking characters (rn instead of m), adding extra words before the domain (secure-ledger-verification.com), or using subdomains that seem legitimate (ledger.secure-accounts.net where "ledger" is just a subdomain of a scam site).
Real companies never ask for your seed phrase, private keys, or full passwords through email, SMS, or direct messages.
Recognize pressure tactics and impossible requests
Legitimate services don't create artificial urgency or threaten immediate account closure without multiple prior warnings. Messages claiming "verify within 24 hours or lose access" or "urgent security action required" use pressure to bypass your critical thinking. Real platforms give you time to respond and provide multiple communication channels for verification.
Any request for your seed phrase, private keys, or signing transactions through links reveals a scam immediately. No legitimate wallet provider, exchange, or blockchain service ever needs this information. Hardware wallet companies specifically tell you they'll never contact you asking to verify your device through seed phrase entry.
What to do if you clicked or shared info
Acting quickly after clicking a phishing link or sharing credentials determines whether you can minimize damage. The first minutes after realizing you've been compromised offer your best opportunity to protect remaining assets and prevent further theft. Understanding how phishing works includes knowing the immediate steps that can save your funds when prevention fails. Panic wastes time, systematic action saves what's left.
Immediate actions for damage control
Disconnect from the internet immediately if you entered your seed phrase or private keys on a suspicious site. Attackers often execute transfers within minutes of capturing wallet access credentials. Cutting your connection buys you seconds to move funds to a new wallet before they can. For exchange accounts, change your password instantly using a different device that you know is secure.
Transfer all remaining cryptocurrency to a completely new wallet that uses a fresh seed phrase you've never shared anywhere. Generate this new wallet on a device you trust or a hardware wallet if you have one available. Every second counts because automated theft scripts can drain balances faster than manual transfers. Don't move funds back to the compromised wallet later, consider it permanently tainted.
Speed matters more than perfection when assets are actively at risk.
Securing your accounts and devices
Enable or update two-factor authentication on all exchange accounts using an authenticator app rather than SMS. Change passwords for every service that uses the same credentials you exposed. Run a full antivirus scan on any device where you clicked suspicious links because some phishing attacks install malware alongside credential theft.
Reporting and preventing future attacks
Report the phishing attempt to the impersonated platform so they can warn other users and take down fake domains. Contact your exchange's security team if you shared exchange credentials. Document everything: the original message, the fake website URL, and timestamps of when you interacted with the scam. This information helps both platform security teams and law enforcement track attacker infrastructure. Consider the compromised wallet permanently unsafe and plan to abandon it completely after moving all assets.
Key takeaways and next steps
Understanding how phishing works gives you the defensive advantage you need to protect your cryptocurrency holdings. Attackers rely on emotional triggers, visual deception, and time pressure to bypass your critical thinking. Your best defense combines healthy skepticism with verification habits: always check sender addresses, examine URLs before clicking, and remember that no legitimate service ever requests your seed phrase or private keys through messages.
Hardware wallets eliminate most phishing risks by keeping your private keys offline where remote attackers cannot reach them. Even if you accidentally enter credentials on a fake website, hardware devices require physical confirmation for every transaction. Cold storage protects you from the majority of online threats that target exchange accounts and software wallets.
Take the next step toward comprehensive security by exploring cold storage solutions at FinTech Dynasty. Moving your assets to hardware protection removes you from the primary attack surface that phishers exploit, and proper cold storage implementation ensures your wealth remains under your exclusive control.
