
Multisig Wallet Meaning: How It Works And When To Use It
Share
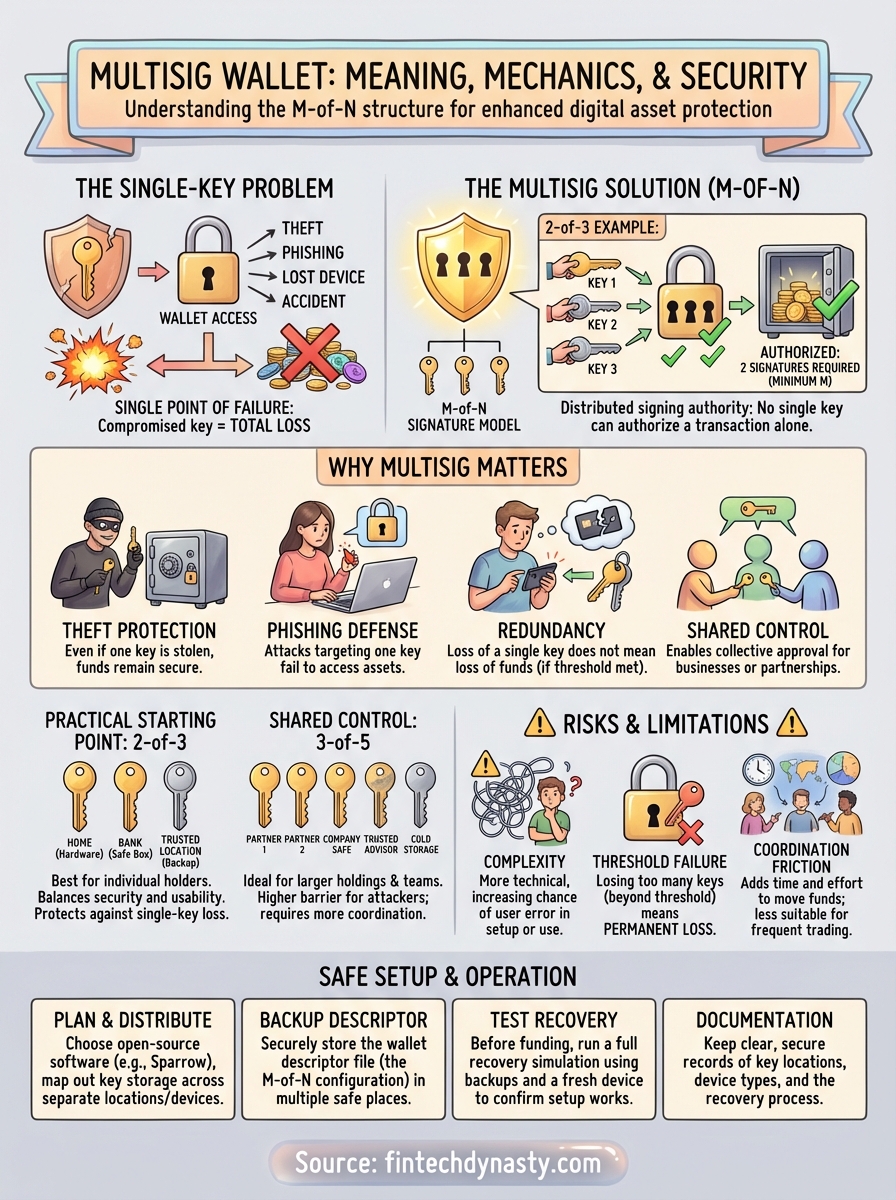
A standard crypto wallet relies on a single private key. If that key gets compromised, or lost, your funds are gone. The multisig wallet meaning is straightforward: it's a wallet that requires multiple private keys to sign off on a transaction before it can go through. This extra step creates a security barrier that no single point of failure can break.
At FinTech Dynasty, we help crypto holders understand the tools that make self-custody safer and more practical. Multisig technology sits at the intersection of personal security and shared control, making it one of the most reliable methods for protecting digital assets. Whether you're an individual looking to eliminate single-key risk or part of a team that needs collective approval over funds, multisig wallets offer a proven structure worth understanding.
This article explains how multisig wallets actually work under the hood, walks through the most common configurations like 2-of-3 and 3-of-5, and covers the specific scenarios where they make the most sense. You'll also learn about the tradeoffs involved, because multisig isn't the right fit for everyone. By the end, you'll know exactly what a multisig wallet does, how it compares to standard single-key setups, and whether it belongs in your self-custody strategy.
Why multisig wallets matter in crypto security
Single-key wallets are the default in crypto, but they carry a fundamental flaw: one compromised key means total and permanent loss. There is no recovery process, no customer service line, and no way to reverse a transaction once it clears. For anyone holding a meaningful amount of cryptocurrency, that exposure deserves serious attention, and understanding the multisig wallet meaning is one of the most direct ways to address it.
The single-key problem
Every standard wallet assigns you one private key that controls all funds inside it. That key might live on a hardware device, a software app, or a piece of paper in a drawer. Regardless of where it lives, if someone steals it, guesses it, or tricks you into revealing it, they gain full and immediate access to your funds. You lose everything with no way to reverse it.
Physical and digital threats target single-key setups in very different ways. A house fire, flood, or physical theft can destroy a hardware wallet and wipe out access entirely. A phishing attack, malware infection, or social engineering attempt can extract your key without you realizing it until your balance reads zero. The single point of failure is not a theoretical edge case. It is the most documented and consistent reason people lose funds permanently in self-custody.
A single compromised key is all it takes to drain a standard wallet completely, with no recourse and no reversal possible.
What multisig protects against
Multisig wallets distribute signing authority across multiple keys, so that no single key is enough to authorize a transaction on its own. This structure removes the single point of failure entirely. An attacker who gains access to one of your keys cannot move your funds without also controlling the required number of additional keys defined by your setup.
This protection covers several concrete and realistic situations:
- Theft or physical breach: A stolen device gives an attacker only one key, which is not enough to complete a transaction.
- Phishing or remote attacks: Clicking a malicious link or running compromised software may expose one key, but the attacker still cannot reach your funds.
- Lost or damaged hardware: Losing one key does not mean losing your funds, provided the remaining keys meet the required signing threshold.
- Shared fund control: In a business or partnership, multisig prevents any single person from unilaterally moving funds without others approving the transaction.
Each of these scenarios represents a real, documented risk. Multisig does not eliminate human error, but it raises the barrier for any attack to succeed by a significant margin.
Why multisig matters for self-custody specifically
Self-custody means you hold your own private keys without depending on a third party. That independence gives you full control, but it also places the entire security burden on you alone. A single mistake, a single lost device, or a single successful phishing attempt can result in total loss with no safety net underneath you.
Multisig shifts the model from "protect one key perfectly at all times" to "protect multiple keys across separate locations, devices, and methods." That distinction has real consequences. You can store one key on a hardware wallet, a second on a separate device, and keep a third in a geographically distinct physical location. An attacker would need to breach all of those simultaneously, which is far harder to pull off than targeting a single point.
For long-term holders who are not moving funds frequently, this setup fits naturally. Your funds can remain in a multisig wallet for months or years with minimal interaction required while staying far more resistant to the threats that have caused the most permanent losses in the history of crypto self-custody.
How multisig wallets work
Multisig wallets use a specific cryptographic structure where multiple private keys are required to authorize a transaction. The wallet itself is not controlled by one key file or one device. Instead, it is generated from a combination of keys, and spending from it requires a defined number of those keys to sign together. Understanding this structure is what brings the multisig wallet meaning from an abstract concept into something practical you can apply.
The M-of-N signature model
The core structure of any multisig wallet is described as M-of-N, where N is the total number of keys involved and M is the minimum number of signatures required to approve a transaction. A 2-of-3 setup means you hold three keys total, and any two of them must sign before a transaction goes through. A 3-of-5 setup means five keys exist and three must sign.
The M-of-N model gives you direct control over both the total number of keys and the signing threshold, so you can tune the wallet to fit your exact security needs.
This flexibility matters in practice. A lower signing threshold like 2-of-3 makes the wallet more accessible if you lose one key, since the remaining two are still enough to move funds. A higher threshold like 3-of-5 creates a much harder target for an attacker, because they would need to compromise three separate keys before gaining any access at all.
What happens during a transaction
When you initiate a transaction from a multisig wallet, it does not complete immediately. The transaction is created and broadcast as a partially signed object, sitting in an incomplete state until enough co-signers add their signatures. Each key holder reviews the transaction details independently and signs using their own device and their own key, without needing to share keys with anyone else.
Once the required number of valid signatures accumulates, the transaction becomes fully authorized and gets submitted to the network for confirmation. The enforcement happens at the protocol level. On Bitcoin, for example, Bitcoin Script handles the on-chain logic that checks whether the required number of legitimate signatures are present before accepting the transaction as valid. This means the rules are enforced by the blockchain itself, not by any single software tool or intermediary you have to trust.
Common multisig setups and when to use them
The M-of-N model gives you a range of configurations to choose from, and picking the right one depends on your specific situation. Understanding the multisig wallet meaning in practice means knowing which setup fits your threat model, how many keys you can realistically manage, and how often you actually need to access your funds. Not every configuration makes sense for every person.
2-of-3: The most practical starting point
For individual holders, 2-of-3 is the most widely used multisig configuration, and for good reason. You hold three keys total, and any two of them can authorize a transaction. This balance between security and usability works well for people who want protection against losing a single key without adding unnecessary complexity to their setup.
A common approach is to store one key on a hardware wallet at home, a second on a separate hardware device at a trusted location like a bank safe deposit box, and a third in a geographically distinct secure location you control. If one key is lost, stolen, or destroyed, your two remaining keys still give you full access to your funds. If an attacker compromises one key, they still cannot move anything without the second.
A 2-of-3 setup removes the single-key risk while keeping recovery straightforward, making it the best entry point for most self-custody holders.
3-of-5: Built for larger holdings and shared control
Stepping up to a 3-of-5 configuration raises the bar significantly. You hold five keys, and three signatures are required before any transaction completes. This setup makes the most sense when you are managing a larger amount of cryptocurrency that justifies the added operational complexity, or when multiple people need to share custody of pooled funds.
Businesses, investment partnerships, and family trusts use 3-of-5 setups to ensure no single person can unilaterally drain an account. You can distribute keys across five separate holders or locations, and an attacker would need to compromise three of them simultaneously to access anything. That is a far more difficult target than any single-key or 2-of-3 arrangement.
Choosing the right setup for your situation
Your choice should come down to two core factors: how much you hold and how many keys you can realistically keep track of. If you are a solo holder with a moderate amount in cold storage, 2-of-3 is almost always the right answer. If you manage shared funds or hold a significant sum that warrants extra redundancy, 3-of-5 gives you stronger protection without becoming unmanageable.
Risks and limitations you need to know
Understanding the multisig wallet meaning also requires an honest look at where it falls short. Multisig improves your security posture significantly, but it introduces new categories of risk that a standard single-key wallet does not carry. Ignoring these tradeoffs can leave you in a worse position than if you had never set up multisig at all.
Complexity raises the chance of user error
Multisig wallets are more technically demanding than single-key setups, and that complexity is itself a risk. You need to correctly configure the M-of-N parameters, back up every key separately, and understand how each piece fits together before you ever store funds. A misconfigured wallet, a poorly stored backup, or a misunderstood signing process can result in permanent loss, not from an attacker, but from your own setup mistakes.
The most common cause of permanent fund loss in multisig is not theft. It is user error during setup or recovery.
Before you fund any multisig wallet, run full test transactions using small amounts and practice the recovery process from scratch using only your backups. This confirms your setup actually works before real money is at stake.
Losing too many keys locks you out permanently
The M-of-N structure protects you when you lose one key, but losing more keys than your threshold allows means you lose access to your funds permanently. In a 2-of-3 setup, losing two keys leaves you with only one, which is not enough to authorize a transaction. No recovery process exists at that point, and no support team can help you.
You need a deliberate key storage strategy that accounts for physical disasters, theft, and long-term accessibility. Each key should be stored in a separate, secure location with clear documentation of its role in your setup. Storing all keys in the same place defeats the entire purpose of multisig and reintroduces the single-point-of-failure problem you were trying to solve.
Coordination adds friction to every transaction
Each transaction requires gathering the required number of signatures, which takes more time and effort than simply approving a payment from a single-key wallet. If your co-signers are spread across different locations or devices, routine transactions can become slow and logistically complicated. For active traders or anyone who moves funds frequently, this friction is a real operational cost.
Multisig is best suited for funds you hold long-term and rarely need to access quickly. For day-to-day spending or active trading, a simpler hot wallet with strong security practices will serve you better than a multisig arrangement that creates delays every time you need to act fast.
How to set up and run multisig safely
Setting up a multisig wallet correctly requires careful planning before you touch any software or move any funds. The multisig wallet meaning becomes fully practical only when your key distribution, software choice, and recovery documentation all work together as a coherent system. Rushing the setup is one of the fastest ways to create a wallet that looks functional but fails the moment you actually need it.
Choose your software and key distribution plan
Your first decision is which software you will use to create and manage your multisig wallet. Sparrow Wallet (for Bitcoin) and similar open-source tools let you construct a multisig setup using multiple hardware wallets as your key signers. Each key should live on a separate hardware device from a separate manufacturer when possible, so a firmware vulnerability on one device does not compromise your entire signing setup.
Once you select your software, map out where each key will live before you generate anything. Write down which key goes to which location, what device holds it, and how a trusted person could access that information in an emergency. Clear, documented key distribution prevents the confusion that causes permanent loss during a recovery attempt.
Every key in your multisig setup needs its own documented backup strategy, stored separately from the other keys.
Back up your wallet descriptor file
Most people focus on backing up private keys but overlook the wallet descriptor file, which is the configuration file that defines your M-of-N structure and links your keys together. Without this file, you cannot reconstruct your wallet even if all your private keys are intact. Store the descriptor in at least two separate secure locations, kept apart from where you store your individual keys.
Treat the descriptor backup as seriously as the keys themselves. A hardware failure or software update can erase your wallet configuration, leaving you with keys that unlock nothing because you have no record of how they connect. Print a copy, store a second copy encrypted on a USB drive, and confirm both copies are accessible before you fund the wallet.
Run a full recovery test before funding
Before sending any significant amount into your multisig wallet, simulate a complete recovery using only your backups and a fresh device. Wipe your primary setup, restore from your stored backups, and confirm the wallet reconstructs correctly with all keys visible and functional. This test is the only reliable way to confirm your setup actually works under real conditions.
Skipping this step is the single most common reason people discover a broken setup only after they have already moved funds in with no way to recover them.
Conclusion
The multisig wallet meaning comes down to one core principle: spreading signing authority across multiple keys so that no single failure, whether theft, loss, or a compromised device, can drain your funds. You now understand how M-of-N configurations work, which setup fits your situation, and what risks you need to manage carefully before moving any funds in.
Putting this into practice takes deliberate planning. Your key distribution, descriptor backup, and recovery test all need to work together before you fund anything. Skipping any of those steps creates a false sense of security that can be worse than using a standard wallet.
If you want to go deeper on hardware wallet options, storage security, and building a complete self-custody setup from the ground up, explore our full crypto security guides at FinTech Dynasty. Every resource on the site is built to help you protect your assets with clear, practical information and no speculation attached.
